It would be highly unusual to find any modern software with no bugs or security holes in it. When found, software makers will often offer patches to update the software. Unless these patches are applied you may be at risk if you use the software.
Operating system updates are particularly important to apply. The operating system in the computer (be it Windows, OS/X, or some Linux form) controls everything going on in the computer. This means that security holes found in the operating system can be serious; particularly when they can be exploited to take over the computer and cause it to do something bad (like, perhaps, joining a botnet). Often these update patches are issued shortly after the security hole is found but before an exploit is available. Unfortunately, some patches are not available until after the security hole is found and exploited. These latter are often called Zero Day Attacks![]() and can be serious if the exploit is spreading rapidly.
and can be serious if the exploit is spreading rapidly.
Fortunately, most operating systems have a method of distributing these updates to people automatically as they are issued. Unfortunately, most operating systems allow the user to turn this update process off and many do. Also, scheduling of operating system updates varies. Microsoft, for example, has a monthly patch Tuesday where the majority of patches are issued. Some patches are issued out of sequence; these include frequent updates to malware scanning databases and important updates that close a serious zero-day attack hole. Apple typically waits for longer periods and issues a very large number of patches at the same time. Other operating systems vary and some require you to check for any patches instead of having an automatic process for notification.
When an operating system collects enough update patches, the collection is put together into a service pack (Microsoft’s terminology). The service pack can also include other updates to the operating system to give it new capabilities.
Software patches/updates are not new. Early patches were issued on punched cards or paper tape. They moved to magnetic tape and other media as mass media changed.
Patches can be small or large and, after or during application, may require the computer to be restarted to properly apply. It’s important when patching the operating system to not be doing anything important so that if the computer needs to be restarted that can happen without loss of important data.
While individual users can usually apply security patches without problem, corporate users may not. Often a corporate data system is fully integrated with the operating system so that any patches to the operating system must be first tested by the computer support department to look for problems introduced by the patch itself. This may require a standalone network where patches are applied and tested in an environment not connected to the main network.
Individual software programs also often have patches that the manufacturer develops. Often these only appear in program updates that may or may not be free and sometimes, even if free, are hard to find as a software maker may not have an automatic notification system established or, if they do, the customer may not have registered their copy of the software into that system. Also, even if such a system exists, users change E-mail addresses and update mailings sent out may never be received. If you have software that you depend on it’s important to register that software with the manufacturer and keep that registration up to date in order to get important notices.
Software is not the only -ware that can have security holes. The firmware that controls many devices typically has a form of software built into the hardware. Sometimes this code is in a form that can be updated by rewriting the entire firmware chip. The BIOS on a motherboard is a good example of such firmware. The patch in these cases usually means running some special program designed to completely rewrite the chip. These patches must be applied very carefully and version numbers verified as different patches will apply to different firmware versions. Applying the wrong patch to firmware can render the device inoperable (called “bricking” the device).
Windows Update
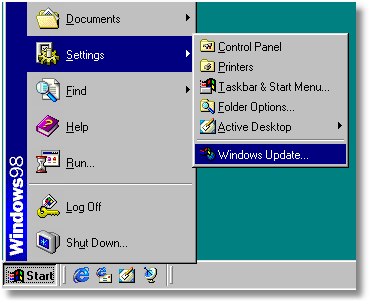
From Windows 98 on, Internet Explorer has had a link to the Windows Update service at Microsoft’s website. While it started largely as a method of sending users added material (e.g., themes, games, device driver updates, etc.) patches started to be sent to users via Windows Update as well. The link started in the Settings menu of Windows 98 (see screenshot) and has since migrated to various other locations in the Start menu with different versions of Windows. Windows Vista, Server 2008, and Windows 7 have a Control Panel applet which allows you to tailor the Windows Update process. You can set the updates to happen automatically as detected, have the updates downloaded but not installed until you tell Windows to, have Windows just notify you when an update is available but do nothing else until you tell it, or, the most dangerous option, perform no updates at all.
For automatic updates other than the routine malware detection databases Windows will install almost daily Microsoft will generally send them out on the second Tuesday of each month; called Patch Tuesday. Important updates may be available at other times in order to fix special security holes. An option at Windows Update will also set the parameters for updates to other Microsoft software. This schedule can, now and again, cause problems for users. If there are a significant number of updates issued on Patch Tuesday then the Microsoft servers can have problems keeping up with the flood of data being requested. That means that some updates are not necessarily all sent to the computer at the same time nor installed at the same time. This has led some to find that when they turn their computer off, an update will delay the shutdown process for some significant time. This can happen even if Windows Update is set to not do automatic updates and ask for your permission. A Microsoft help bulletin![]() describes the problem.
describes the problem.
One thing to note: Windows Update uses Microsoft’s MSHTML layout engine and ActiveX controls and is therefore generally limited to use with Internet Explorer or browsers that are compatible with IE. Starting with Windows Vista Windows Update uses Transactional NTFS as part of the install as this feature of the NTFS file system allows changes to be committed to the file system all at once instead of incrementally. This makes it easier to recover from problems during the update process.
And, if all else fails, you can go directly to Microsoft’s update site using this URL: http://update.microsoft.com/![]()
Each update is accompanied by a bulletin. The collection of Microsoft’s update bulletins can be found here: http://www.microsoft.com/protect/computer/updates/bulletins/default.mspx![]()
Program Updates
Before you can determine what you need to update you have to know what exactly is installed on your system. You can, of course, manually run through the installed programs menu off of the Windows Start button but it’s easier to run a program to do that work for you and produce a report.
One free tool for doing so is the Belarc Advisor![]() . The Belarc Advisor builds a detailed profile of your installed software and hardware, missing Microsoft hotfixes, anti-virus status, CIS (Center for Internet Security) benchmarks if appropriate for your operating system, and displays the results in your Web browser. Known hotfixes you have not installed are highlighted in the report. All of your PC profile information is kept private on your PC. Belarc Advisor is licensed for personal use only. Contact the company for their network or corporate software.
. The Belarc Advisor builds a detailed profile of your installed software and hardware, missing Microsoft hotfixes, anti-virus status, CIS (Center for Internet Security) benchmarks if appropriate for your operating system, and displays the results in your Web browser. Known hotfixes you have not installed are highlighted in the report. All of your PC profile information is kept private on your PC. Belarc Advisor is licensed for personal use only. Contact the company for their network or corporate software.
Another tool you can use to see what vulnerabilities might be lurking as the Secunia Personal Software Inspector![]() . The program will both catalog programs and highlight those with known vulnerabilities. The patches necessary are highlighted.
. The program will both catalog programs and highlight those with known vulnerabilities. The patches necessary are highlighted.
Summary
It would be highly unusual to find any modern software with no bugs or security holes in it.
- Operating systems are especially vulnerable since they interact with the entire computer at a basic level.
- Programs can also have holes and need to be kept up to date. Tools are available to help with this.
- The word in the title is repeated three times because it’s so important.
| Safe Computing Practices | Outlook and Outlook Express |
Comments from original:
sid brown
Said this on 2009-10-30 At 02:53 pm
need a download checker and download manager to seguence and do downloads in EST TIME OF 2 AM TO 7 AM.
Any free ware desired, but will pay for inexpensive.
boxedquad.
#3
DaBoss
Said this on 2009-10-30 At 03:19 pm
In reply to #2
I don’t use them but a quick Google search brought up a number of free download managers. Just looking at the site briefly, the one called “Free Download Manager” seems to be a good fit to the requirements.
http://www.freedownloadmanager.org/